Codetown
Codetown ::: a software developer's community
May 2017 Blog Posts (4)
 Add a Caption to an Image
Add a Caption to an Image
The ability to Interpret image data using software is advancing fast! The two images above are captioned with program generated text. Here's an article that describes concepts and an approach to generate a caption for an image. The code is written in Python and uses TensorFlow. …
ContinueAdded by Michael Levin on May 25, 2017 at 8:57am — No Comments
 The JHipster Mini Book ::: Free!
The JHipster Mini Book ::: Free!
This is what I'm reading right now. Here you go! Matt has given us good presentations that are quick and to the point. Super cool! If you decide to pay $19.95 for the printed book, it'll cover about 3 craft pints. The health monitor app Matt made will record one less point. You'll see! Enjoy, and be sure to let Matt know how much you appreciate this free mini…
Added by Michael Levin on May 18, 2017 at 2:30pm — No Comments
 $11 Billion Swapmeet
$11 Billion Swapmeet
First of all, relax, I'm not announcing an exclusive executive swapmeet. The market for used cell phones has ramped up to a whopping $11 billion as of 2016[1]. That's a big number by itself, especially since the market scarcely existed just ten years ago. By comparison, everything sold in every category by everyone worldwide on Ebay, new or used, was $84 billion total in 2016[2].
Unless you are actually a senior exec and can offer your device, refurbished, to other…
ContinueAdded by Ismail Jones on May 15, 2017 at 8:36pm — No Comments
 Cross-Platform Mobile Development
Cross-Platform Mobile Development
Mobile devices prove to be a setback for cross-platform software development, but I hope it will be a minor one. At present, Android totally dominates the mobile market both in terms of hardware and software volume. As well, mobile devices are overtaking desktops for overall usage as we speak. But Linux, as open-source-friendly as it is appears to be getting the rub from Google, so where are we?
As Google continues to grumble about not controlling the world, they're leaking…
ContinueAdded by Ismail Jones on May 14, 2017 at 9:24am — No Comments
Featured Blog Posts
Latest Blog Posts
- New Java features
- Free Eclipse book, recently published
- What is vibe coding?
- You can now download the source code that sparked the AI boom
- 50% Keyboard Guide: Tiny Typists' Delight
- Software language criteria
- We have some exciting news to share with you. Otavio will be joining us to discuss the latest version of Camel in an exclusive presentation. Presentation Details: Speaker: Otavio Rodolfo Piske Topic:…
Most Popular Blog Posts
Monthly Archives
2025
2024
- June (1)
2023
2022
2021
2020
2019
- December (1)
- November (1)
- October (1)
- September (1)
- August (2)
- July (1)
- June (4)
- May (1)
- March (2)
- February (1)
- January (2)
2018
2017
2016
- December (18)
- November (10)
- September (3)
- August (1)
- July (3)
- June (7)
- May (6)
- April (5)
- March (2)
- February (2)
- January (4)
2015
- December (4)
- November (2)
- October (2)
- August (1)
- July (2)
- June (1)
- April (2)
- March (6)
- February (1)
- January (6)
2014
2013
2012
- December (5)
- October (3)
- September (4)
- August (1)
- July (4)
- June (4)
- May (1)
- April (3)
- March (4)
- February (7)
- January (3)
2011
- December (1)
- November (7)
- October (6)
- September (7)
- August (3)
- July (9)
- June (5)
- May (7)
- April (2)
- March (2)
- February (3)
- January (4)
2010
- December (6)
- November (3)
- October (2)
- August (6)
- July (1)
- May (4)
- April (3)
- March (11)
- February (5)
- January (13)
2009
- December (10)
- November (4)
- October (7)
- September (4)
- August (5)
- July (2)
- June (3)
- May (9)
- April (2)
- March (8)
- February (3)
- January (1)
2008
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
Airbnb Implements Context-Aware Identity Model to Support Privacy-First Social Features
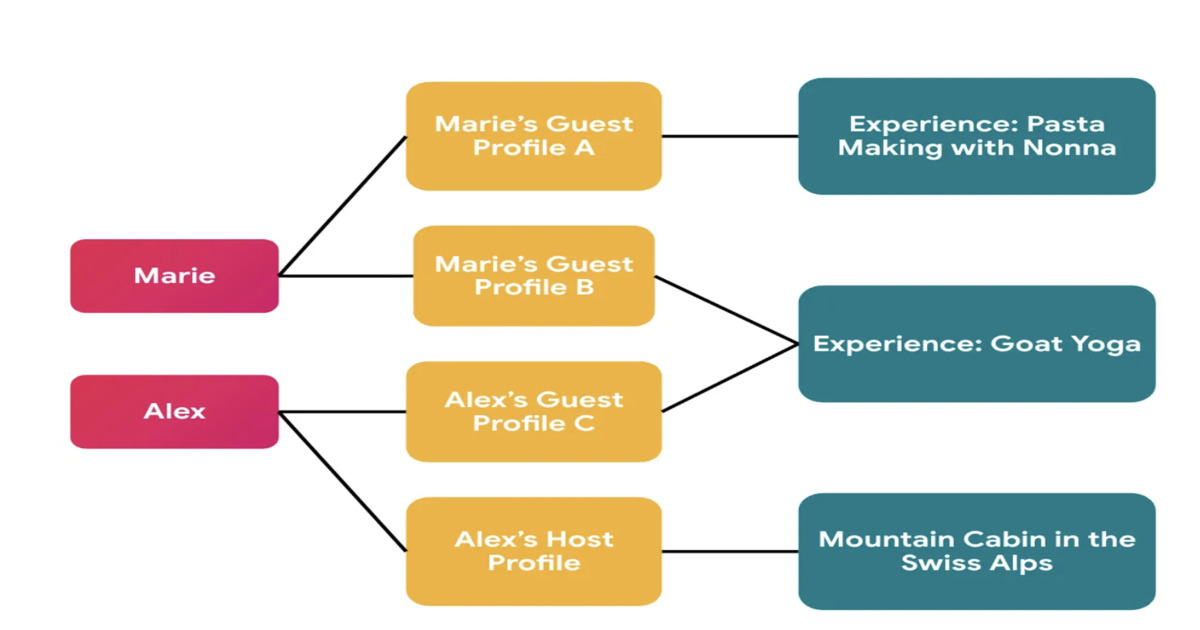
Airbnb has redesigned its identity system to support privacy-first social features in Experiences. The platform introduces context-specific profiles that separate global user identity from externally visible profiles, preventing cross-context linkage. The migration leveraged automated auditing, manual validation, and AI-assisted refactoring to enforce correct identity usage across services.
By Leela KumiliJEP 533 Tightens Exception Handling in Java's Structured Concurrency for JDK 27

JEP 533, Structured Concurrency, has reached integrated status for JDK 27. It refines exception handling and type safety in its API, particularly focusing on exception flow with a new ExecutionException type. Changes include an updated Joiner interface and a new open overload for easier configuration. The steady evolution signals ongoing development as feedback shapes the API.
By A N M Bazlur RahmanPresentation: What I Learned Building Multi-Agent Systems From Scratch

Paulo Arruda discusses Shopify’s evolution in AI adoption, moving from simple chat tools to a sophisticated swarm of specialized agents. He explains the transition from massive "all-in-one" prompts to lean, narrow-focused agent microservices that slash task times from hours to minutes. He also shares a future-looking hypothesis on using filesystem-based adapters to solve context bloat.
By Paulo ArrudaArticle: The Mathematics of Backlogs: Capacity Planning for Queue Recovery

Backlogs in distributed systems are arithmetic problems, not mysteries. This article provides practical formulas for calculating backlog drain time, sizing consumer headroom, and setting auto-scaling triggers. It covers key failure modes — retry amplification, metastable states, and cascading pipeline bottlenecks — plus when to shed load instead of draining.
By Rajesh Kumar PandeyGrafana's Pyroscope 2.0 Makes Continuous Profiling Practical at Scale

Grafana Labs has launched Pyroscope 2.0, a rearchitected open-source continuous profiling database. This version improves storage costs, query performance, and operational complexity. Key changes include single write paths for profiles, stateless query processing, and enhanced capabilities for profiling data. It supports the OpenTelemetry Protocol, aligning with current trends in observability.
By Matt Saunders
© 2026 Created by Michael Levin.
Powered by
![]()