Codetown
Codetown ::: a software developer's community
October 2012 Blog Posts (3)
 Nighthacking ...with Steven Chin and company (and featuring James Gosling)
Nighthacking ...with Steven Chin and company (and featuring James Gosling)
I have a virtual event to announce that you can participate in online called the NightHacking Tour.
Steven Chin is a friend and colleague of mine. He's a Java…
ContinueAdded by Michael Levin on October 23, 2012 at 6:00am — No Comments
 GatorJUG November Meeting - JEE6 and CDI with Curtis McMillen
GatorJUG November Meeting - JEE6 and CDI with Curtis McMillen
 Got CDI? Wonder what dependency injection and JEE6 are all about? What the heck is Spring? RSVP, por favor. This is an event you won't want to miss! Check it out here and please RSVP so we'll know how much pizza to order. Invite your…
Got CDI? Wonder what dependency injection and JEE6 are all about? What the heck is Spring? RSVP, por favor. This is an event you won't want to miss! Check it out here and please RSVP so we'll know how much pizza to order. Invite your…
Added by Michael Levin on October 16, 2012 at 8:11am — 1 Comment
 GatorJUG October Meeting
GatorJUG October Meeting
A good time was had by all at our October GatorJUG meeting. Kevin Neelands discussed Android Design Patterns in the context of his recent work on the job with an Android app. The lessons learned he presented were not just interesting but huge timesavers for him. They also dramatically…
Added by Michael Levin on October 15, 2012 at 7:00am — No Comments
Featured Blog Posts
Latest Blog Posts
- New Java features
- Free Eclipse book, recently published
- What is vibe coding?
- You can now download the source code that sparked the AI boom
- 50% Keyboard Guide: Tiny Typists' Delight
- Software language criteria
- We have some exciting news to share with you. Otavio will be joining us to discuss the latest version of Camel in an exclusive presentation. Presentation Details: Speaker: Otavio Rodolfo Piske Topic:…
Most Popular Blog Posts
Monthly Archives
2025
2024
- June (1)
2023
2022
2021
2020
2019
- December (1)
- November (1)
- October (1)
- September (1)
- August (2)
- July (1)
- June (4)
- May (1)
- March (2)
- February (1)
- January (2)
2018
2017
2016
- December (18)
- November (10)
- September (3)
- August (1)
- July (3)
- June (7)
- May (6)
- April (5)
- March (2)
- February (2)
- January (4)
2015
- December (4)
- November (2)
- October (2)
- August (1)
- July (2)
- June (1)
- April (2)
- March (6)
- February (1)
- January (6)
2014
2013
2012
- December (5)
- October (3)
- September (4)
- August (1)
- July (4)
- June (4)
- May (1)
- April (3)
- March (4)
- February (7)
- January (3)
2011
- December (1)
- November (7)
- October (6)
- September (7)
- August (3)
- July (9)
- June (5)
- May (7)
- April (2)
- March (2)
- February (3)
- January (4)
2010
- December (6)
- November (3)
- October (2)
- August (6)
- July (1)
- May (4)
- April (3)
- March (11)
- February (5)
- January (13)
2009
- December (10)
- November (4)
- October (7)
- September (4)
- August (5)
- July (2)
- June (3)
- May (9)
- April (2)
- March (8)
- February (3)
- January (1)
2008
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
Kubernetes v1.36: Security Defaults Tighten as AI Workload Support Matures

Kubernetes v1.36, released in 2026, includes 70 enhancements focused on security, AI workloads, and API scalability. Key features graduating to General Availability are User Namespaces, Mutating Admission Policies, and Fine-Grained Kubelet API Authorization. The release also addresses workload management and introduces new features for AI resource allocations.
By Matt SaundersAnthropic Launches Claude Platform on AWS
Anthropic has announced the general availability of Claude Platform on AWS, a new deployment option that gives AWS customers direct access to Anthropic’s native Claude platform using AWS authentication, billing, and monitoring services.
By Daniel DominguezAirbnb Implements Context-Aware Identity Model to Support Privacy-First Social Features
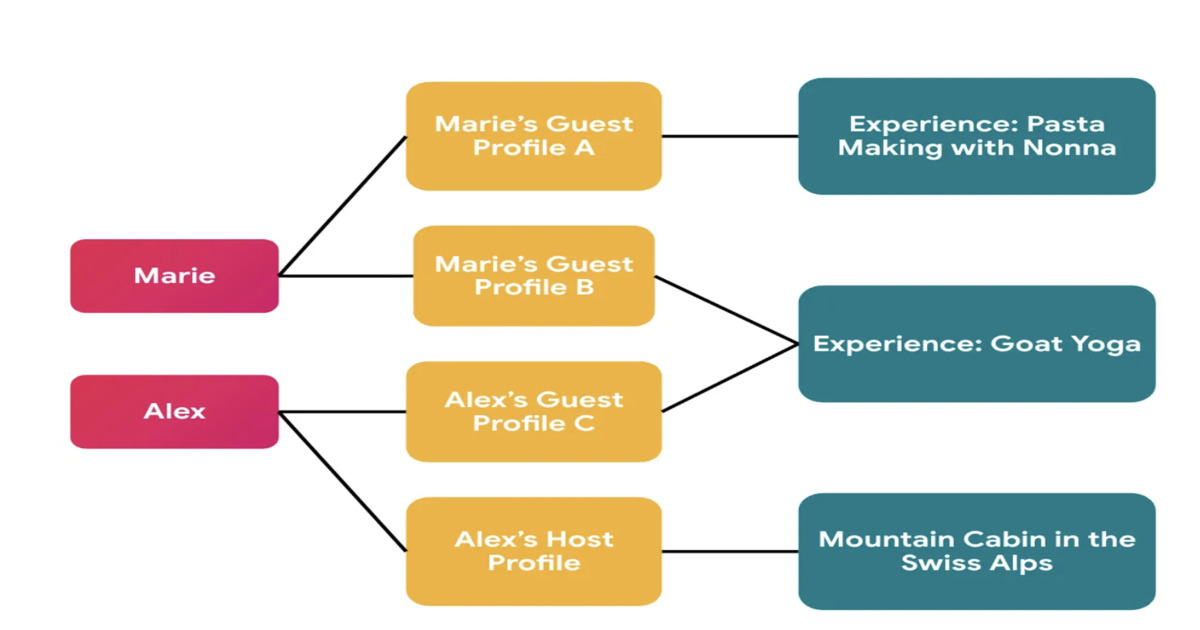
Airbnb has redesigned its identity system to support privacy-first social features in Experiences. The platform introduces context-specific profiles that separate global user identity from externally visible profiles, preventing cross-context linkage. The migration leveraged automated auditing, manual validation, and AI-assisted refactoring to enforce correct identity usage across services.
By Leela KumiliJEP 533 Tightens Exception Handling in Java's Structured Concurrency for JDK 27

JEP 533, Structured Concurrency, has reached integrated status for JDK 27. It refines exception handling and type safety in its API, particularly focusing on exception flow with a new ExecutionException type. Changes include an updated Joiner interface and a new open overload for easier configuration. The steady evolution signals ongoing development as feedback shapes the API.
By A N M Bazlur RahmanPresentation: What I Learned Building Multi-Agent Systems From Scratch

Paulo Arruda discusses Shopify’s evolution in AI adoption, moving from simple chat tools to a sophisticated swarm of specialized agents. He explains the transition from massive "all-in-one" prompts to lean, narrow-focused agent microservices that slash task times from hours to minutes. He also shares a future-looking hypothesis on using filesystem-based adapters to solve context bloat.
By Paulo Arruda
© 2026 Created by Michael Levin.
Powered by
![]()