Codetown
Codetown ::: a software developer's community
This just in from Luis Espinal of MJUG:
The EasyB syntax for writing stories and specifications is a lot more succinct than the one provided by Specs, the Scala BDD framework (at least when looked upon from a 10K foot view)
Regards,
Tags:
Replies to This Discussion
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
Claude Code Used to Find Remotely Exploitable Linux Kernel Vulnerability Hidden for 23 Years

Anthropic researcher Nicholas Carlini used Claude Code to find a remotely exploitable heap buffer overflow in the Linux kernel's NFS driver, undiscovered for 23 years. Five kernel vulnerabilities have been confirmed so far. Linux kernel maintainers report that AI bug reports have recently shifted from slop to legitimate findings, with security lists now receiving 5-10 valid reports daily.
By Steef-Jan WiggersArticle: Using AWS Lambda Extensions to Run Post-Response Telemetry Flush

At Lead Bank, synchronous telemetry flushing caused intermittent exporter stalls to become user-facing 504 gateway timeouts. By leveraging AWS Lambda's Extensions API and goroutine chaining in Go, flush work is moved off the response path, returning responses immediately while preserving full observability without telemetry loss.
By Melvin PhilipsNew Rowhammer Attacks on NVIDIA GPUs Enable Full System Takeover

Security researchers have demonstrated a new class of Rowhammer attacks targeting NVIDIA GPUs that can escalate from memory corruption to full system compromise, marking a significant shift in hardware-level security risks.
By Craig RisiAnthropic Paper Examines Behavioral Impact of Emotion-Like Mechanisms in LLMs
A recent paper from Anthropic examines how large language models internally represent concepts related to emotions and how these representations influence behavior. The work is part of the company’s interpretability research and focuses on analyzing internal activations in Claude Sonnet 4.5 to understand the mechanisms behind model responses better.
By Robert KrzaczyńskiPresentation: Platform Engineering: Lessons from the Rise and Fall of eBay Velocity
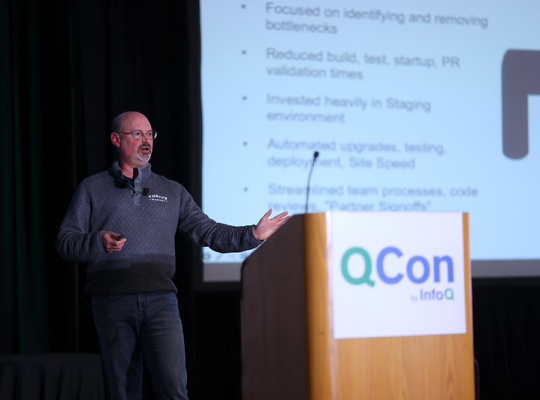
Randy Shoup discusses the "Velocity Initiative," a transformation that doubled engineering productivity and modernized eBay’s DORA metrics. He shares the technical playbook used to scale 4,500 services while explaining why even elite engineering execution can’t save a company hampered by waterfall planning, risk aversion, and a "pathological" culture of fear.
By Randy Shoup
© 2026 Created by Michael Levin.
Powered by
![]()