Codetown
Codetown ::: a software developer's community
-
Mike Bivins
- Male
- United States
- Share on Facebook MySpace Tweet
- Blog Posts (2)
- Discussions (2)
- Events
- Groups (5)
- Photos
- Photo Albums
- Videos
Mike Bivins's Groups
-
Computational Linguistic…
15 members
-
Democratic Republic of C…
8 members
-
Cloud Computing Village
16 members
Mike Bivins's Discussions
JavaFX and Netbeans IDE
Is there any knowledge on the horizon on integrating JavaFX into Netbeans in the same way Swing is integrated into it? Currently, as I know it, you can generated a JavaFX gui - which generates a…Continue
Started Dec 11, 2012
Gifts Received

Mike Bivins has not received any gifts yet
Mike Bivins's Page
Profile Information
- How did you hear about Codetown?
- JUG
- What are your main interests in software development?
- Java JSE development. Learning about J2EE. Developing in PHP and JavaScript among others.
Mike Bivins's Blog
Responsive Web Design? What's that? - Exploring NODE.JS
Posted on February 1, 2013 at 11:13am 0 Comments 1 Like
It may not adhere to the strict Java format of OJUG but was quite useful in learning more of the growing tools available to the web based developer.
Jackie Gleason answered this and unlocked other mysteries when he explained what NODE.JS was about. Including a demo where he started a .js server, Jackie showed us how to set up an Express Project Layout worked starting with NPM and yielding to his own "Hello World" page. He continued by showing us how document styled db could be…
FLEX goes to Apache
Posted on January 22, 2013 at 12:02pm 0 Comments 1 Like
Not familiar with FLEX but this article has some interesting info on it. Another tool in the web developer's toolbox?
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
AWS Releases Next Generation of Amazon OpenSearch Serverless

Amazon Web Services has recently announced the general availability of the next generation of Amazon OpenSearch Serverless, with a redesigned architecture that enables 20 times faster resource provisioning than the previous serverless architecture, true scale-to-zero capability, and up to 60% lower cost than a provisioned cluster for peak loads.
By Gianmarco NalinPinterest Uses Content Fingerprints for URL Deduplication Across Millions of Domains
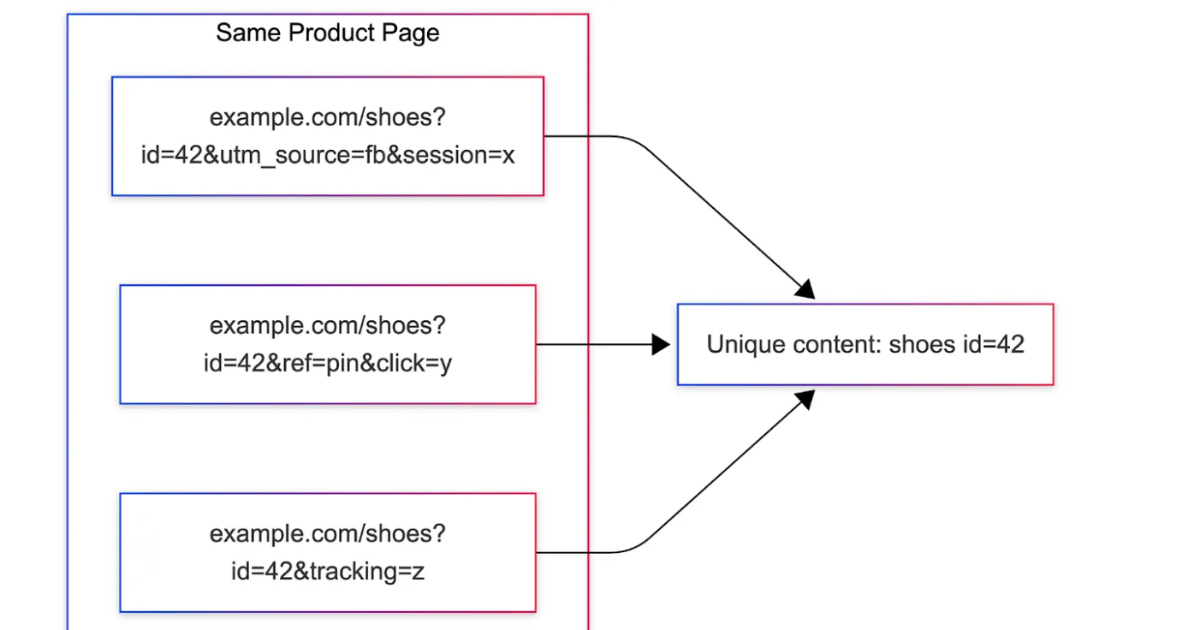
Pinterest introduced MIQPS, a URL normalization system that identifies which query parameters affect page identity using rendered content fingerprints. It reduces duplicate processing across millions of domains by replacing rule-based approaches with offline analysis, anomaly detection, and runtime parameter maps, improving ingestion efficiency and scalability in large-scale content pipelines.
By Leela KumiliJava News Roundup: JDK 27 in Rampdown, JDK 28 Expert Group, GlassFish, Infinispan, Kotlin

This week's Java roundup for June 1st, 2026, features news highlighting: JDK 27 in Rampdown Phase One; the formation of the JDK 28 Expert Group; the GlassFish Arquillian Connectors Suite for Jakarta EE TCKs; point releases for Infinispan and Kotlin; maintenance releases of GlassFish and Micronaut; and the June 2026 beta release of Open Liberty.
By Michael RedlichGemma 4 12B Enables On-Device, Multimodal Agentic Workflows with an Encoder-free Architecture

Google says Gemma 4 12B is "designed to bring agentic, multimodal intelligence directly to your laptop", further noting that the new model can be combined with Google AI Edge to "build and experiment locally, on everyday machines". This integration allows for a wide range of capabilities, from autonomous data processing to generating visual insights and even building webpages or executing tools.
By Sergio De SimoneCelebrating 20 Years of InfoQ

InfoQ celebrates its 20th anniversary. To mark the occasion, we have published a walk-through of the trends InfoQ called early, where they sit on the adoption curve today, and how that curve may evolve over the next decade.
By InfoQ
© 2026 Created by Michael Levin.
Powered by
![]()
Comment Wall (1 comment)
You need to be a member of Codetown to add comments!
Join Codetown
If someone with multiple personalities threatens suicide, is that considered a hostage situation?