Codetown
Codetown ::: a software developer's community
Java 8 Resources (thanks to Mattias Karlsson)
Guess you know about all the resources and video cast Oracle provided
at the Java 8 Launch site:
http://www.oracle.com/events/us/en/java8/index.html
On top of that we have released all Java 8 talks from Jfokus 2014
including the Keynote with Georges Saab and Mark Reinhold.
Except the talks from a number of Oracle speakers you can find these
and many more:
-Java 8 Language Capabilities - What's in it for you?, Venkat Subramaniam
-Lambda Expressions: Myths and Mistakes, Richard Warburton
-Navigating the Stream API, Maurice Naftalin
They are now freely available here:
http://www.parleys.com/search/jfokus
OR with your iPad or Android device...
The Jfokus 2014 Play App enables you to watch talks from Jfokus in the
hammock or while commuting to work. The application has support for
off-line mode so now you can download the entire presentation.
Application "Jfokus 2014 Play" is available for iPad and Android.
Links to each app can be found here:
Android: https://play.google.com/store/apps/details?id=com.parleys.android.j...
iPad: https://itunes.apple.com/us/app/jfokus-2014-play/id824139300
Feel free to share these with your JUG members.
To the future and beyond,
Mattias Karlsson
www.linkedin.com/in/mattiask
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
How OpenAI Built a Secure Windows Sandbox for Codex Agents
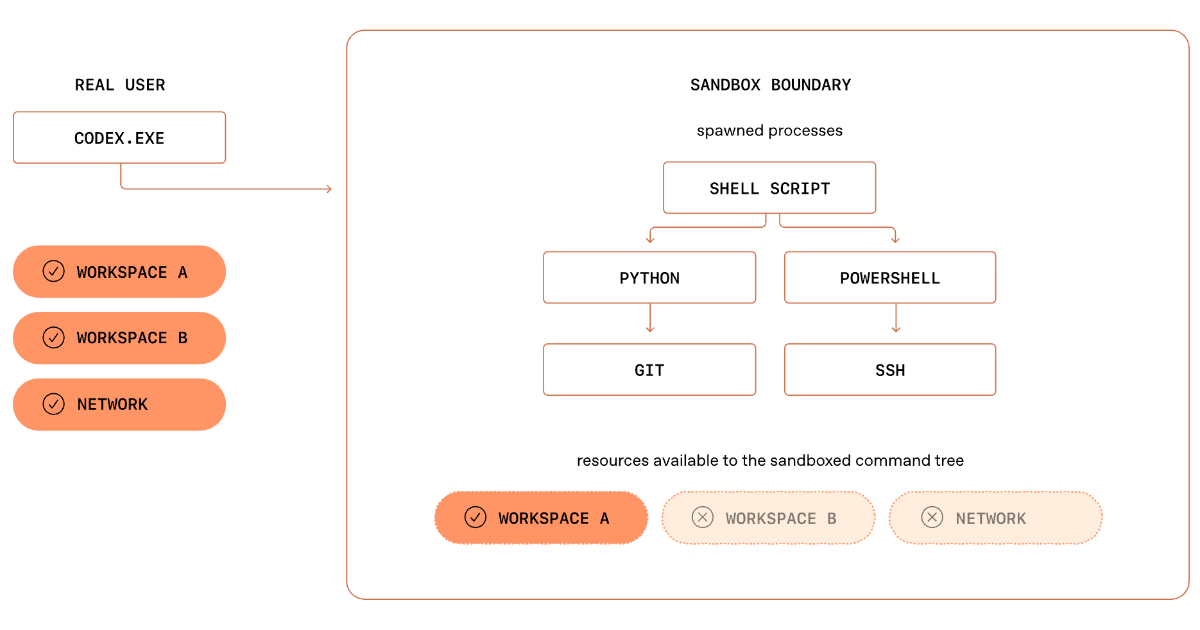
OpenAI details Codex Windows sandbox architecture, showing how SIDs, ACLs, restricted tokens, and dedicated sandbox accounts enable safe execution of autonomous coding tasks. The design balances isolation with real developer workflows and shows how OS security primitives must be composed for AI agents on local development environments.
By Leela KumiliPresentation: Platform Teams Enabling AI - MCP/Multi-Agentic Tools Across Linkedin
LinkedIn’s Karthik Ramgopal and Prince Valluri discuss leveraging AI as a new execution model for large-scale engineering. They explain how to move beyond fragmented implementations by building platform abstractions for orchestration, structured context, and safe tooling like MCP. They share architectural insights from real-world coding, observation, and UI testing agents built at LinkedIn.
By Karthik Ramgopal, Prince ValluriHow Netflix Maps Thousands of Microservices in Real-Time

Netflix has shared details about Service Topology. This internal system creates and updates a live dependency graph for thousands of microservices. It helps engineers see how services connect and resolve issues more quickly. The system merges three separate data sources into a single, queryable graph. It updates almost in real-time as traffic patterns shift.
By Claudio MasoloDropbox Introduces Nova, an Internal Platform for Running AI Coding Agents at Scale

Dropbox has unveiled Nova, an internal platform designed to orchestrate and operationalize AI coding agents across the company's engineering workflows.
By Craig RisiGoogle LiteRT-LM Speeds Up Local Inference Up to 2.2x With Gemma 4 Multi-Token Prediction

LiteRT-LM brings native support for Gemma 4 Multi-Token Prediction (MTP) drafters, enabling up to 2.2x faster inference. The framework is expanding beyond Kotlin and C++ adding support for new Swift and a JavaScript APIs.
By Sergio De Simone
© 2026 Created by Michael Levin.
Powered by
![]()
You need to be a member of Codetown to add comments!
Join Codetown