Codetown
Codetown ::: a software developer's community
Future Internet Architecture Meeting & Webinar
CISE invites you to attend an information meeting and webinar to announce and answer questions concerning its recently released solicitation, Future Internet Architecture-Next Phase (FIA-NP: NSF 13-538) on Monday, February 11, 2013, 1:00 PM to 2:30 PM EDT. You must register at https://mmancusa.webex.com/mmancusa/j.php?ED=200243927&RG=1&... to participate.
CISE plans to support research that builds upon its current investments in Future Internet Architectures (FIA) with the Future Internet Architecture-Next Phase (FIA-NP) solicitation. Proposals are expected to specify research activities that will take existing FIA designs from basic components that have been integrated into early prototypes that demonstrate architectural principles and requirements to more sophisticated architectures with demonstrated prototype systems.
The FIA-NP information meeting will be held February 11, 2013, 1:00PM - 2:30PM EST (10:00 - 11:30 PST)
You may attend the informational meeting either on site or via live webinar.
On site: Please come to room 110 at the National Science Foundation, 4201 Wilson Blvd., Arlington, VA. No badges are needed to attend on site.
Live Webinar: Please register to attend the informational meeting via webinar using the link provided below. After your registration is accepted, you will get an email with a URL to join the meeting. Please be sure to join a few minutes before the start of the webinar. This system does not establish a voice connection on your computer; instead, your acceptance message will have a toll-free phone number that you will be prompted to call after joining. Please note that this registration is a manual process; therefore, do not expect an immediate acceptance. Acceptances should be complete by 10:00AM EST Monday 2/11. In the event the number of requests exceeds the capacity, some requests may have to be denied.
Webinar registration deadline: February 10, 2011, 23:59 PDT
Register at: https://mmancusa.webex.com/mmancusa/j.php?ED=200243927&RG=1&...
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
Airbnb Implements Context-Aware Identity Model to Support Privacy-First Social Features
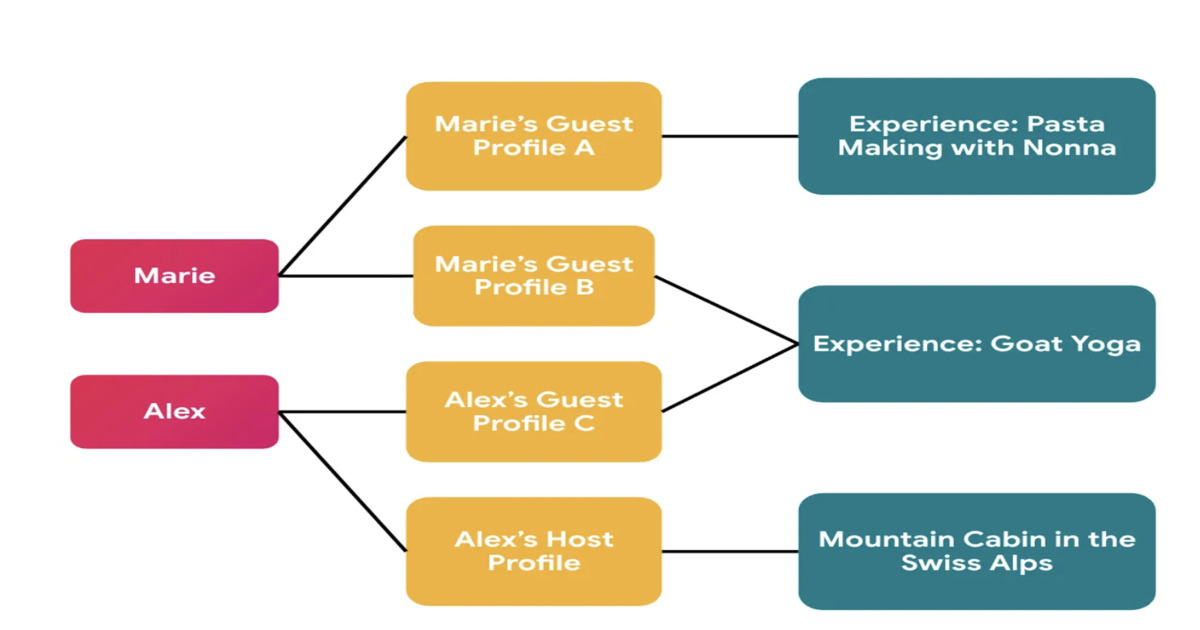
Airbnb has redesigned its identity system to support privacy-first social features in Experiences. The platform introduces context-specific profiles that separate global user identity from externally visible profiles, preventing cross-context linkage. The migration leveraged automated auditing, manual validation, and AI-assisted refactoring to enforce correct identity usage across services.
By Leela KumiliJEP 533 Tightens Exception Handling in Java's Structured Concurrency for JDK 27

JEP 533, Structured Concurrency, has reached integrated status for JDK 27. It refines exception handling and type safety in its API, particularly focusing on exception flow with a new ExecutionException type. Changes include an updated Joiner interface and a new open overload for easier configuration. The steady evolution signals ongoing development as feedback shapes the API.
By A N M Bazlur RahmanPresentation: What I Learned Building Multi-Agent Systems From Scratch

Paulo Arruda discusses Shopify’s evolution in AI adoption, moving from simple chat tools to a sophisticated swarm of specialized agents. He explains the transition from massive "all-in-one" prompts to lean, narrow-focused agent microservices that slash task times from hours to minutes. He also shares a future-looking hypothesis on using filesystem-based adapters to solve context bloat.
By Paulo ArrudaArticle: The Mathematics of Backlogs: Capacity Planning for Queue Recovery

Backlogs in distributed systems are arithmetic problems, not mysteries. This article provides practical formulas for calculating backlog drain time, sizing consumer headroom, and setting auto-scaling triggers. It covers key failure modes — retry amplification, metastable states, and cascading pipeline bottlenecks — plus when to shed load instead of draining.
By Rajesh Kumar PandeyGrafana's Pyroscope 2.0 Makes Continuous Profiling Practical at Scale

Grafana Labs has launched Pyroscope 2.0, a rearchitected open-source continuous profiling database. This version improves storage costs, query performance, and operational complexity. Key changes include single write paths for profiles, stateless query processing, and enhanced capabilities for profiling data. It supports the OpenTelemetry Protocol, aligning with current trends in observability.
By Matt Saunders
© 2026 Created by Michael Levin.
Powered by
![]()

You need to be a member of Codetown to add comments!
Join Codetown