Codetown
Codetown ::: a software developer's community
If you haven't check out Scala lately, go download it's package from http://www.scala-lang.org/downloads/index.html. It can be unzip/untar into a directory like C:\opt for example and can start using.
Here is a quick run with an interpreter that comes with the package:
C:\opt\scala\bin\scala
Welcome to Scala version 2.7.1.final (Java HotSpot(TM) Client VM, Java 1.6.0_10-beta).
Type in expressions to have them evaluated.
Type :help for more information.
scala> new java.util.Date
res0: java.util.Date = Wed Jul 16 21:19:44 EDT 2008
scala> def now = new java.util.Date
now: java.util.Date
scala> now
res1: java.util.Date = Wed Jul 16 21:33:20 EDT 2008
scala> now
res2: java.util.Date = Wed Jul 16 21:33:22 EDT 2008
scala> now
res3: java.util.Date = Wed Jul 16 21:33:23 EDT 2008
scala> val sum = 1 + 2 + 3
sum: Int = 6
scala> val nums = List(1,2,3)
nums: List[Int] = List(1, 2, 3)
scala> nums.foldLeft(0)((sum, n)=> sum+n)
res4: Int = 6
scala> nums.map(n=>Math.pow(n,2))
res5: List[Double] = List(1.0, 4.0, 9.0)
As you can see it's pretty neat to play with Scala collections along with anonlymous functions/closure.
What do you think of Scala Language?
-Z
Tags:
Replies to This Discussion
Notes
Welcome to Codetown!
 Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Codetown is a social network. It's got blogs, forums, groups, personal pages and more! You might think of Codetown as a funky camper van with lots of compartments for your stuff and a great multimedia system, too! Best of all, Codetown has room for all of your friends.
Created by Michael Levin Dec 18, 2008 at 6:56pm. Last updated by Michael Levin May 4, 2018.
Looking for Jobs or Staff?
Check out the Codetown Jobs group.
InfoQ Reading List
ExtendDB: Open Source Amazon DynamoDB Compatible Adapter with Pluggable Storage Backends
AWS recently announced ExtendDB, a DynamoDB-compatible adapter that lets developers use the DynamoDB API with different storage backends, starting with PostgreSQL. The project supports existing SDKs and tools without modification, giving teams greater flexibility to run DynamoDB-style workloads outside of native DynamoDB while maintaining compatibility with current applications and workflows.
By Renato LosioCloudflare Identifies Query Planning Bottleneck in ClickHouse

Cloudflare recently described how a slowdown in its billing pipeline was traced to contention inside the query planning stage of ClickHouse. The team profiled the bottleneck and patched ClickHouse to replace an exclusive lock with a shared lock, drop the per-query copy of the parts list, and improve part filtering.
By Renato LosioHow OpenAI Built a Secure Windows Sandbox for Codex Agents
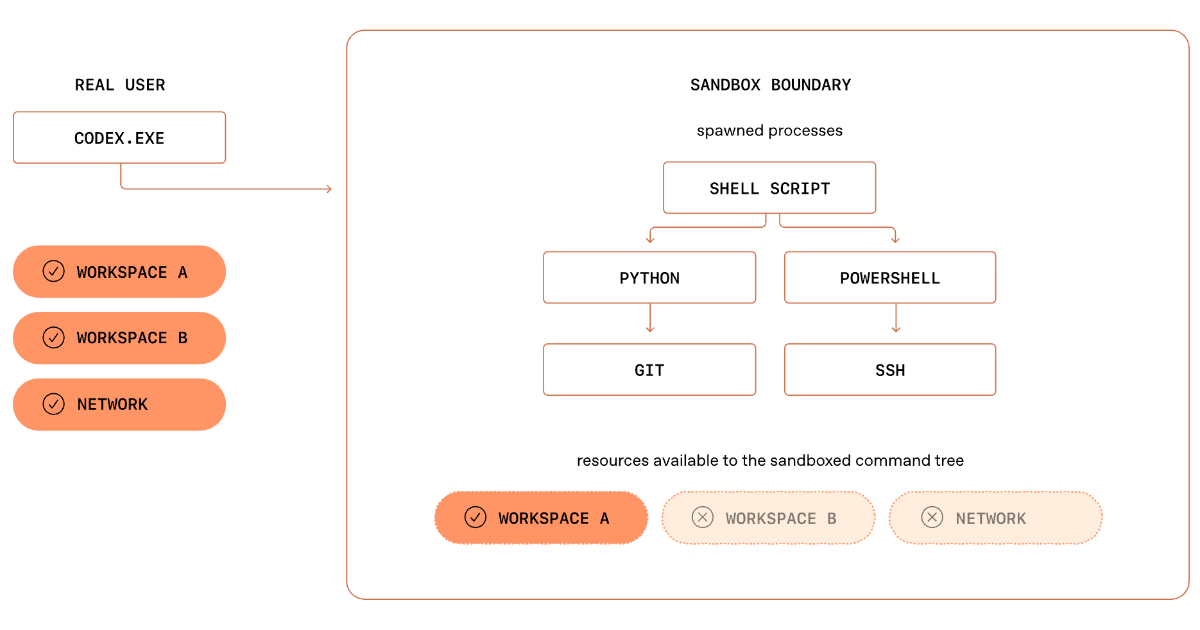
OpenAI details Codex Windows sandbox architecture, showing how SIDs, ACLs, restricted tokens, and dedicated sandbox accounts enable safe execution of autonomous coding tasks. The design balances isolation with real developer workflows and shows how OS security primitives must be composed for AI agents on local development environments.
By Leela KumiliPresentation: Platform Teams Enabling AI - MCP/Multi-Agentic Tools across Linkedin
LinkedIn’s Karthik Ramgopal and Prince Valluri discuss leveraging AI as a new execution model for large-scale engineering. They explain how to move beyond fragmented implementations by building platform abstractions for orchestration, structured context, and safe tooling like MCP. They share architectural insights from real-world coding, observation, and UI testing agents built at LinkedIn.
By Karthik Ramgopal, Prince ValluriHow Netflix Maps Thousands of Microservices in Real-Time

Netflix has shared details about Service Topology. This internal system creates and updates a live dependency graph for thousands of microservices. It helps engineers see how services connect and resolve issues more quickly. The system merges three separate data sources into a single, queryable graph. It updates almost in real-time as traffic patterns shift.
By Claudio MasoloSwitch to the Mobile Optimized View
© 2026 Created by Michael Levin.
Powered by
![]()